

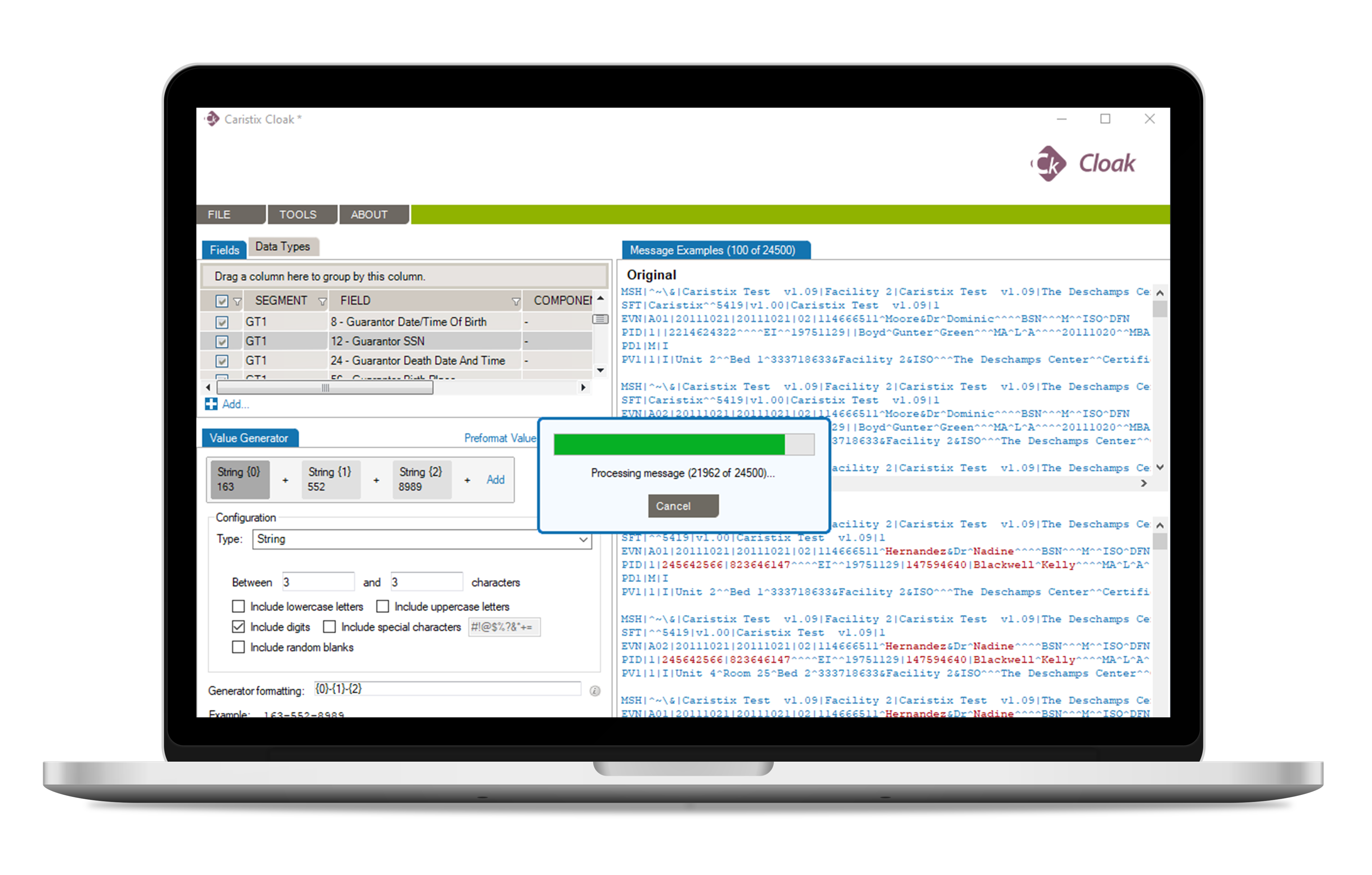
Scrub Protected Patient Health Information (PHI) in HL7® Messages
Collect and share patient data without violating individual privacy laws.
Anonymization, pseudonymization and scrubbing technics of Patient
Health Information (PHI) prevents breach of patient sensitive data.
Capabilities and Features |
Desktop Edition |
Server Edition |
| Compliant with HIPAA-PHI rules | ||
| Safe Harbor and Expert Determination | ||
| Customizable de-identification rules | ||
| Free text de-identification support | ||
| De-identification in batch | ||
| Scale up to millions of HL7 messages | ||
| Download data from your integration engines | ||
| Retrieve data from ODBC database | ||
| De-identify from live feed (real time) | ||
| Web Service deployment |
NORTH AMERICA: +1 (877)-872-0027
WORLD: 1-418-872-4000
EMAIL: info@caristix.com
ASIA-PACIFIC
DENIS CANTIN
T: +61418441388
denis.cantin@caristix.com
NORTH AMERICA & EUROPE
JEAN-LUC MORIN
T: 418 872-4000
jeanluc.morin@caristix.com
HL7® / FHIR® are a registered trademarks of Health Level Seven International. The use of this trademark does not constitute an endorsement by HL7.